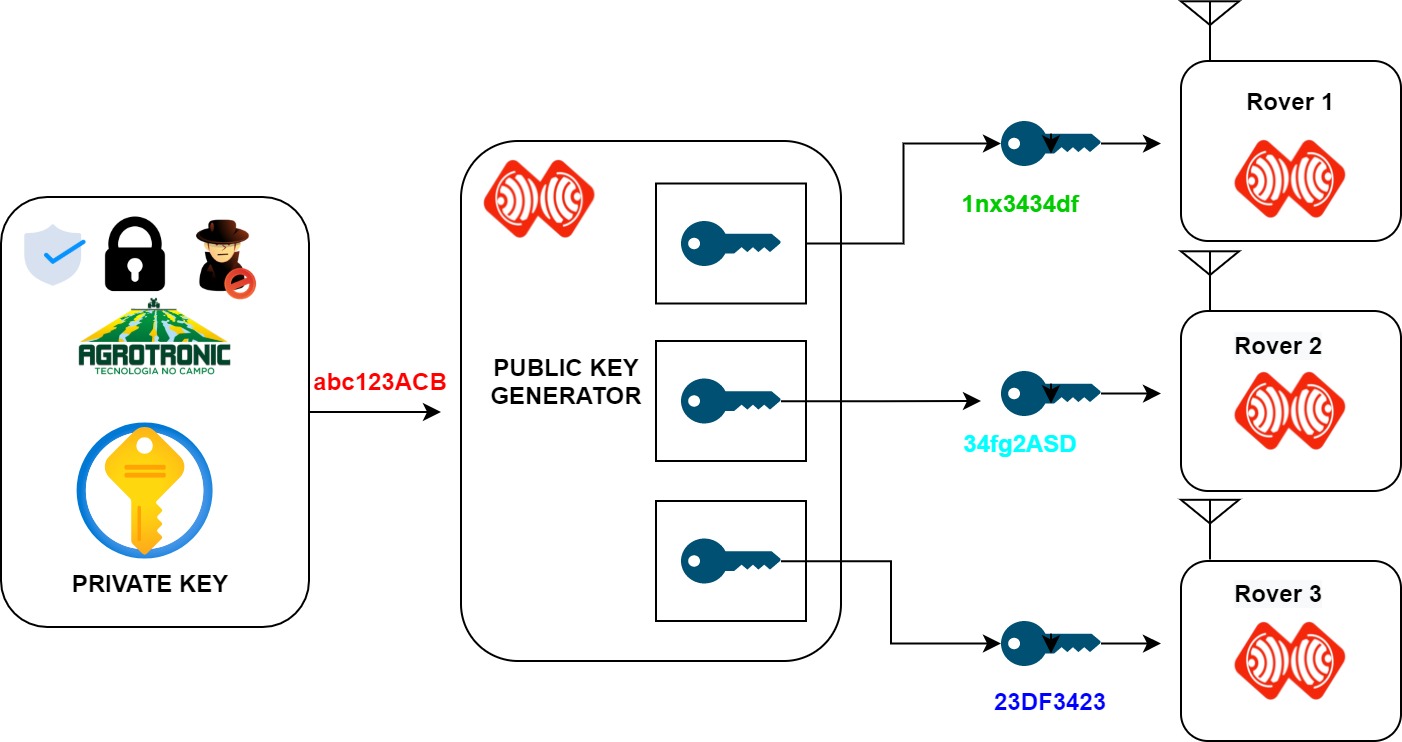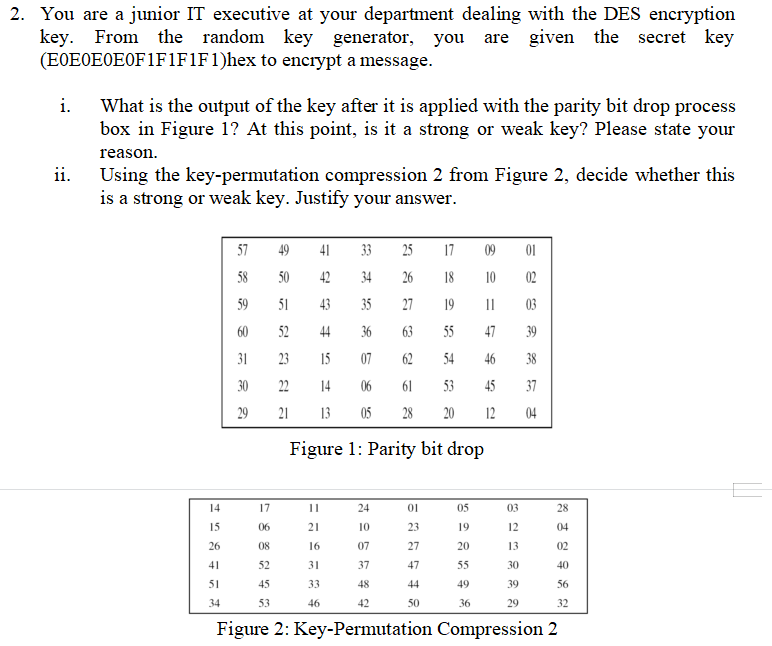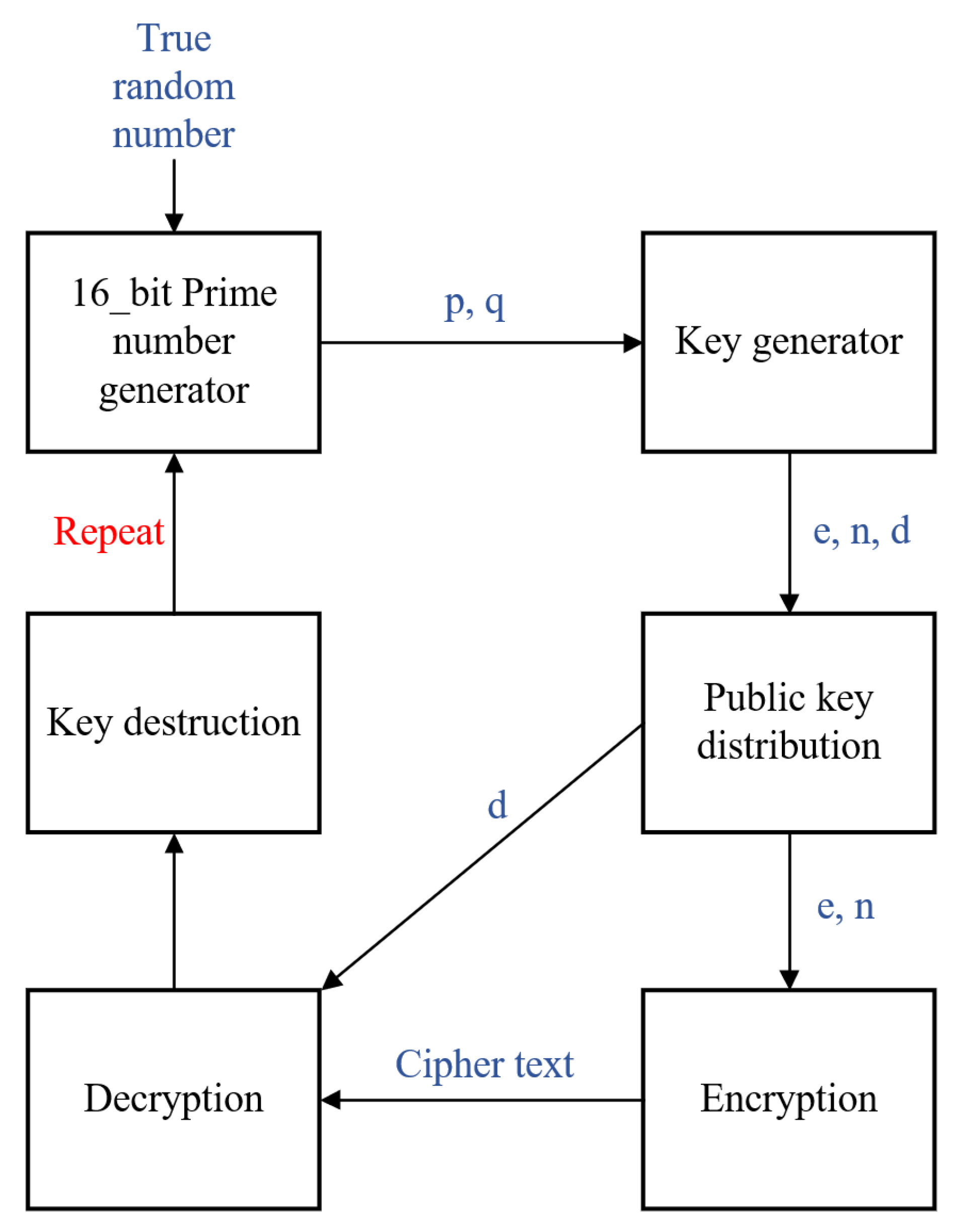
Electronics | Free Full-Text | New RSA Encryption Mechanism Using One-Time Encryption Keys and Unpredictable Bio-Signal for Wireless Communication Devices
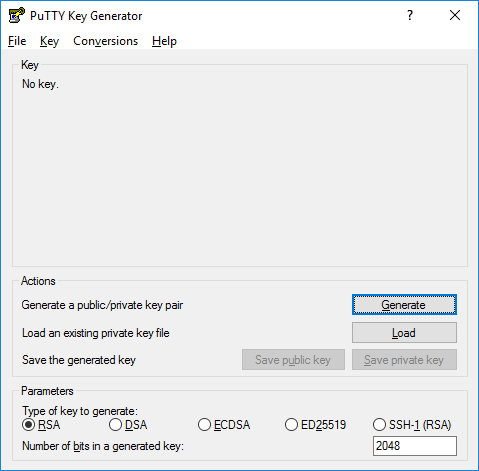
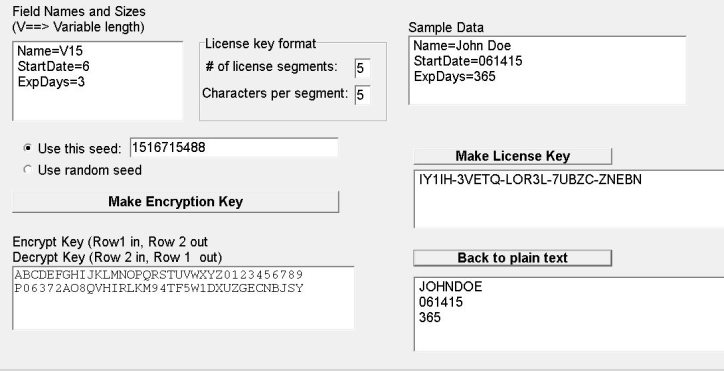
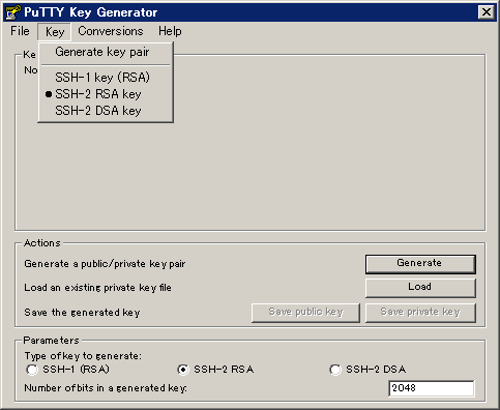
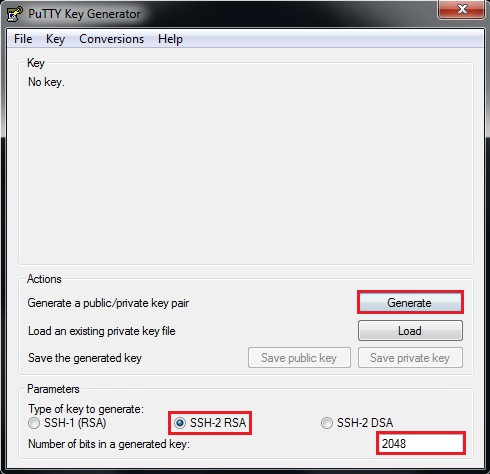
How to install and use puttygen to create new key pairs and change passphrases. Installing keys on server, managing SSH keys.

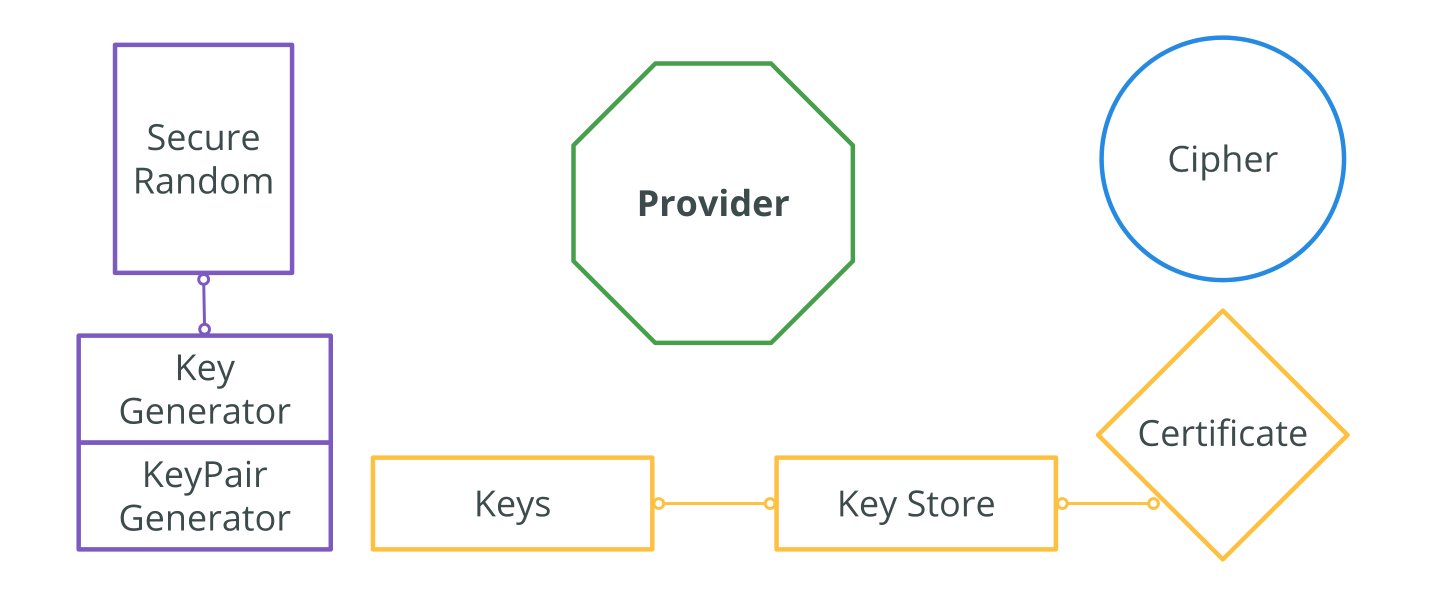
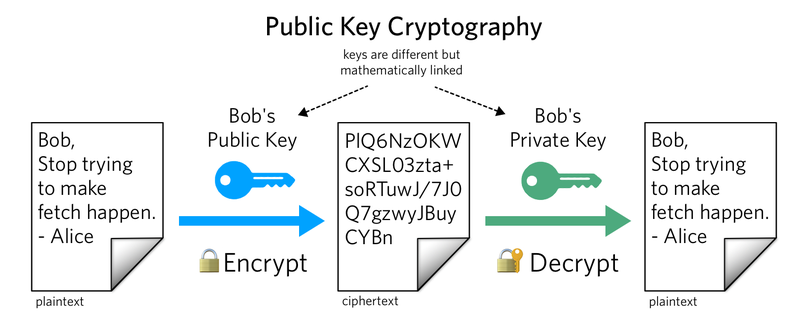
Generation of Cryptographic Keys from Personal Biometrics: An Illustration Based on Fingerprints | IntechOpen




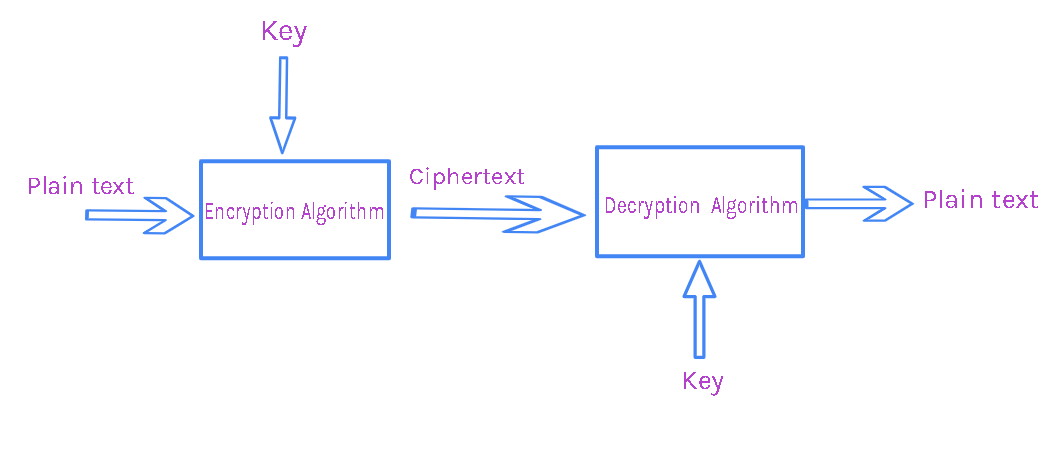
![MS-DRMND]: Content Encryption for AES in Counter Mode | Microsoft Learn MS-DRMND]: Content Encryption for AES in Counter Mode | Microsoft Learn](https://learn.microsoft.com/en-us/openspecs/windows_protocols/ms-drmnd/ms-drmnd_files/image007.png)